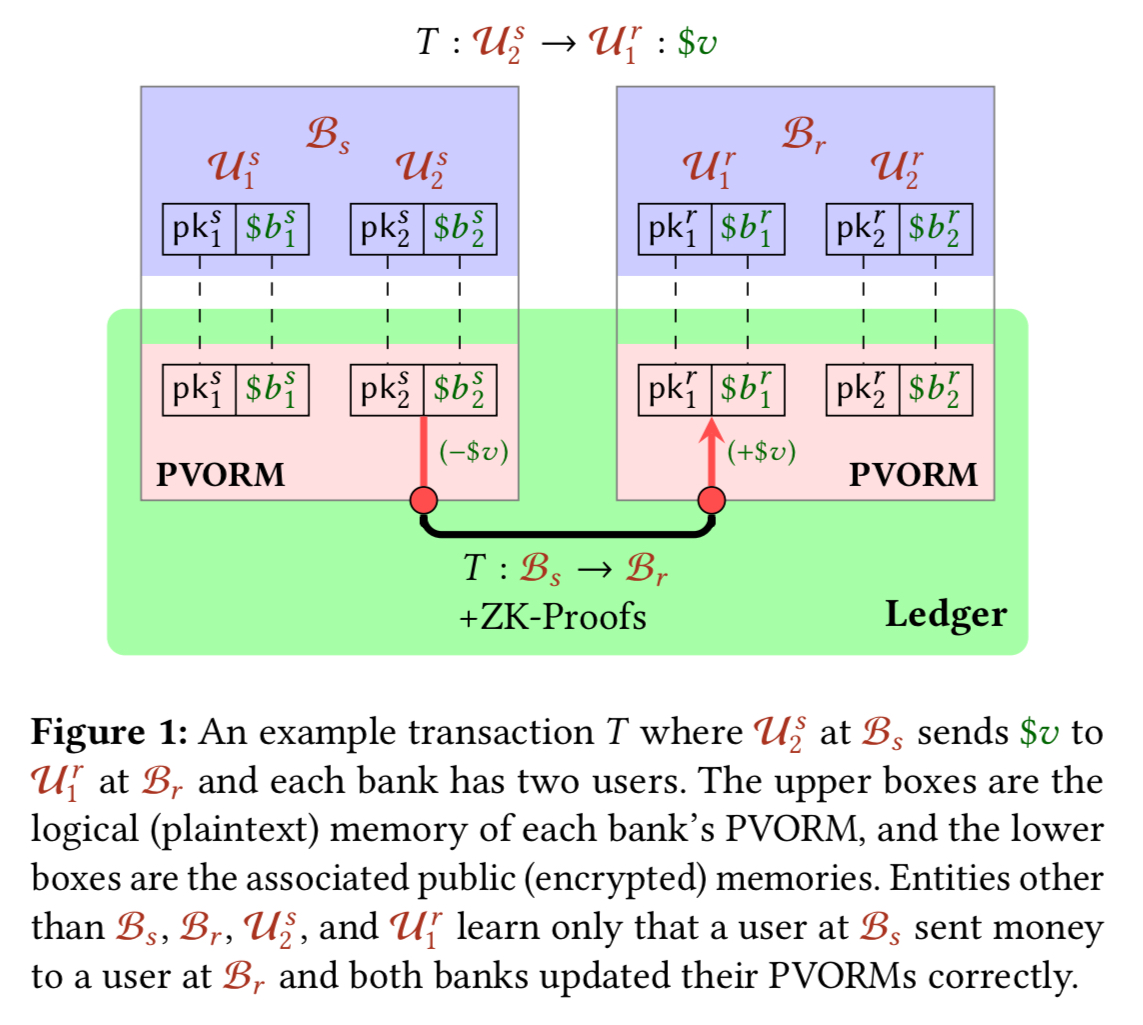
Figure 1 from The Fallacy of Composition of Oblivious RAM and Searchable Encryption | Semantic Scholar
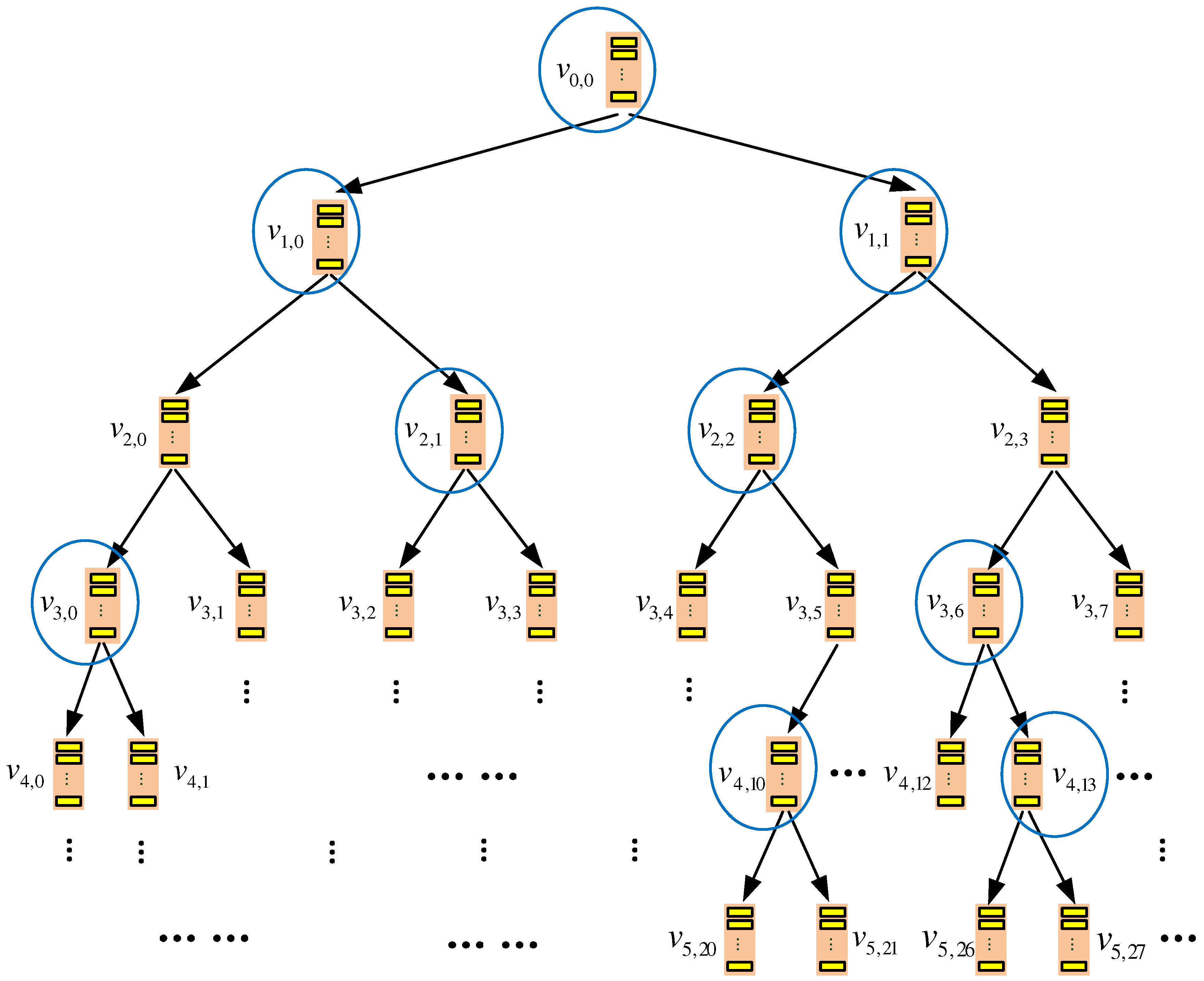
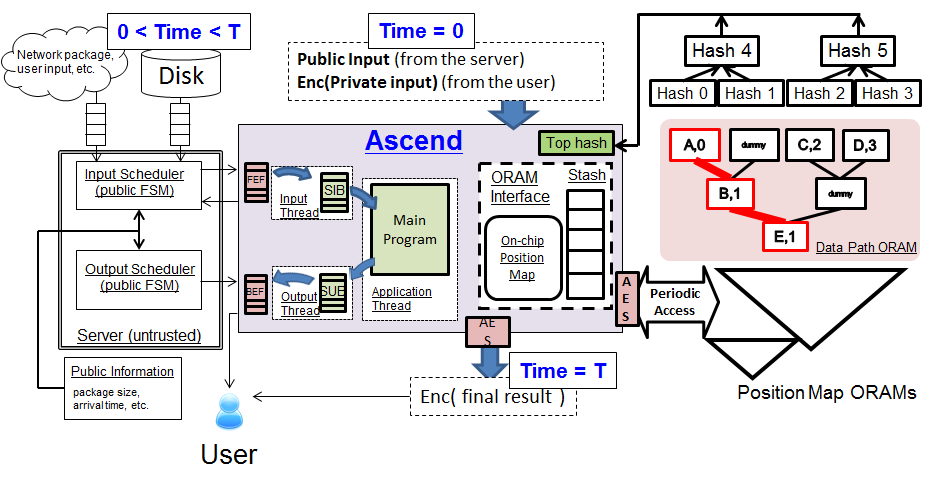
Future Internet | Free Full-Text | TSKT-ORAM: A Two-Server k-ary Tree Oblivious RAM without Homomorphic Encryption
Multi-Client Oblivious RAM with Poly-Logarithmic Communication“ Accepted at Asiacrypt 2020 › Chair of Applied Cryptography







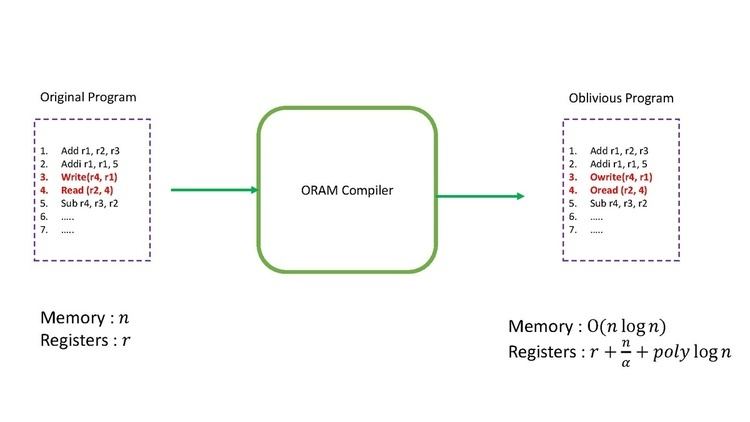
![PDF] PRO-ORAM: Constant Latency Read-Only Oblivious RAM | Semantic Scholar PDF] PRO-ORAM: Constant Latency Read-Only Oblivious RAM | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4524cd3e25d1c965a087e60d60930b8adc34e326/3-Figure1-1.png)

![PDF] The Fallacy of Composition of Oblivious RAM and Searchable Encryption | Semantic Scholar PDF] The Fallacy of Composition of Oblivious RAM and Searchable Encryption | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/a94205aed0148ae6d00986aef009e5e05d046f43/4-Figure3-1.png)